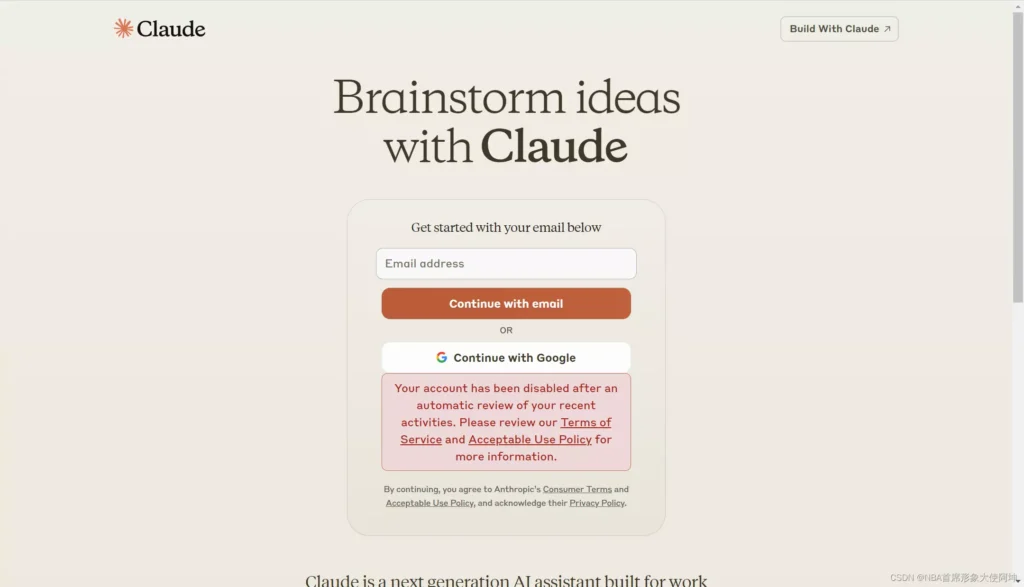
When using Claude, many users encounter account bans or restrictions. Once risk controls are triggered, the success rate of appeals is relatively low. Additionally, the lack of clear official feedback makes it difficult to analyze and fix the root cause.
Therefore, instead of repeatedly appealing after a ban, it is more effective to proactively reduce risks during usage by building a stable user profile to improve overall account credibility.
This article systematically analyzes the underlying reasons behind Claude account bans from a risk control perspective and provides practical optimization strategies to help achieve long-term stable usage within compliance.
I. In-Depth Analysis of Claude Account Ban Reasons
1. Network and IP Environment
In most ban cases, network and IP-related issues account for over 60% and are the primary trigger. The underlying logic can be summarized into four key dimensions:
1.1 Unsupported Regions
According to official guidelines, Claude is only available in supported countries and regions. If accessed from unsupported regions, users may be unable to register or use the service normally.
1.2 Lack of IP Authenticity
Claude’s risk control system is designed to detect automated behavior and evaluates the “authenticity” of an IP. If an IP generates excessive requests in a short period, it may be flagged as automation. High-risk IP types include:
- Data center IPs
- Shared IPs
When multiple users share the same IP, combined with overlapping request patterns, the risk of triggering restrictions increases.
1.3 IP Association Risk
Using shared or mixed network environments may introduce the following issues:
- Poor historical reputation of the IP
- Diverse user behaviors and inconsistent usage patterns
- Low system trust level
New accounts using such IPs may be identified as associated accounts and inherit previous risks.
1.4 Abnormal IP Changes
Claude closely monitors IP stability. High-risk behaviors include:
- Frequent switching between different countries
- Unstable connections causing frequent IP changes
- Mixing rotating residential proxy and data center IP
Real users typically stay in one region for long periods with gradual and reasonable IP changes, which reduces the likelihood of restrictions.
2. Device and Environment Fingerprint
2.1 Device Environment Consistency
Device environment consistency refers to whether system-level information aligns with the IP’s geographic location. Claude checks factors such as:
- IP location
- System language
- Time zone
- Browser locale
2.2 Browser and System Configuration
Beyond macro-level consistency, the system builds a browser fingerprint to identify devices, including:
- Browser type and version
- User Agent (UA)
- Screen resolution and color depth
- Font list and Canvas/WebGL features
- Installed extensions
- Operating system details
3. Usage Behavior Patterns
The system aims to distinguish between human and automated usage.
3.1 API Abuse
Claude enforces limits on usage frequency and access methods. High-risk behaviors include:
- Extremely high request frequency in a short time
- Exceeding normal usage volume
- Automated operations
- Accessing APIs via unofficial channels
3.2 Usage Frequency and Rhythm
In addition to automation, the system evaluates whether usage is reasonable. Normal users typically show:
- Natural intervals between requests
- Realistic usage timing with pauses
- Some level of randomness in behavior
4. Improper Registration Methods
Claude applies strict validation to registration information, focusing on the authenticity and credibility of email and phone numbers. Poor-quality registration may lead to immediate restrictions.
Reliable email: Use real and commonly used services such as Gmail or Outlook. Temporary or low-quality domains may be flagged.
Valid phone number: Use a real number capable of receiving verification codes. Temporary or bulk numbers are considered high risk.
II. Claude Ban Prevention Guide: Practical Strategies for Stable Usage
All prevention strategies can be summarized into one principle:
The system should always perceive you as the same user in the same region, using the same device with consistent behavior.
1. Network and IP Environment
1.1 Ensure IP is Static and Unique
A static proxy should not change automatically. Avoid:
- Rotating proxy
- Shared exit IPs
Recommended practices:
- Use an independently assigned residential proxy
- Disable automatic switching features
- Keep the same IP for each login
1.2 Choose Reliable Network Resources
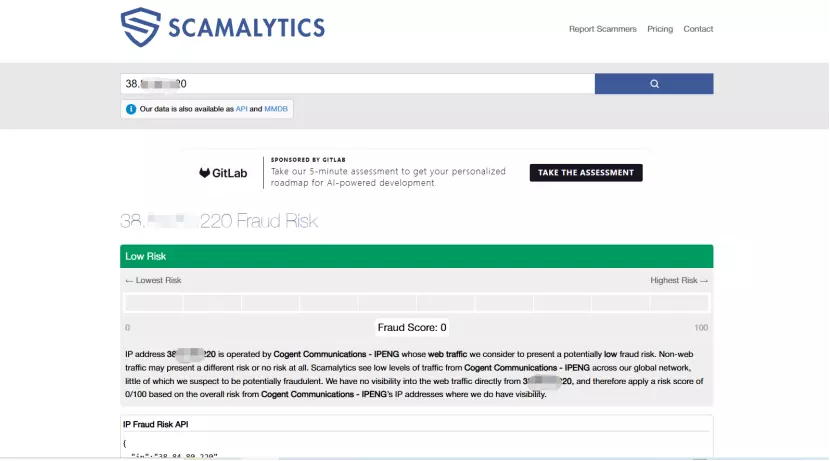
When using proxy services, prioritize providers offering real residential network resources, such as IPFoxy. Key characteristics include:
- IP sourced from real household networks
- Low fraud scores and clean history
Note that some “residential proxy” services may actually be data center IPs in disguise. It is recommended to verify IP quality through detection tools, focusing on blacklist status and fraud scores.
Lower scores generally indicate cleaner IP history and better suitability for long-term use.
1.3 Maintain Region Consistency
During registration and usage, always maintain the same region. For example, if you choose a US node, continue using that region consistently.
Once a stable environment is selected, treat it as a fixed setup and avoid frequent switching. Cross-region changes may be flagged as abnormal behavior.
2. Maintain Device Environment Consistency
2.1 Align Environment Parameters
Ensure system settings match the IP region:
- System language matches region (e.g., English for US IP)
- Time zone aligns with location
- Browser language is consistent
2.2 Stable Device Usage
- Use the same device consistently
- Avoid frequent switching between devices or browsers
- Do not log in from multiple devices within short periods
2.3 Stable Browser Environment
- Use mainstream browsers (Chrome / Firefox)
- Limit extensions, especially those modifying fingerprints
- Avoid frequent resets or cache clearing
2.4 Multi-Account Isolation
- Use separate environments for different accounts
- Avoid sharing browser configurations
- Use an anti-detect browser or separate physical devices when necessary
III. Claude Ban FAQ
Based on practical experience, the stability ranking is:
Official gift credits > Google Pay > Apple gift cards > Direct bank card binding
Non-local bank cards are more likely to trigger verification issues. In addition, once a card is bound, it usually cannot be removed directly and must be replaced. Using someone else’s card may also introduce account association risks. Therefore, it is recommended to prioritize widely supported and mainstream payment methods.
Long-term stability largely depends on the initial account quality during registration. The system evaluates account credibility based on registration data, verification information, and subsequent behavior.
It is recommended to use real and active accounts, ensure reliable verification, and maintain consistent environment and usage patterns. The goal is to always appear as a normal, stable user.
An ideal setup has “native consistency,” meaning the IP location, network exit point, and actual usage environment all align without cross-region routing.
This ensures stable geolocation data, clear network paths, and behavior patterns that resemble real users, reducing the likelihood of triggering risk controls
Conclusion
Claude’s restriction mechanism is not random. It is based on a multi-dimensional evaluation of IP environment, device fingerprint, user behavior, and registration data.
Most risks stem from unstable environments or abnormal behavior. The key is to build a consistent, stable, and explainable user profile, including a fixed region IP, stable device environment, and reasonable usage patterns.
By avoiding high-risk actions and maintaining long-term consistency, accounts can generally achieve safe and sustainable usage.