In the foreign trade and global business industry, LinkedIn is widely regarded as a high-value B2B channel. However, the real challenge lies in long-term safe operation. Many new accounts are restricted during registration or downgraded and suspended in the early warm-up stage due to abnormal behavior.
LinkedIn’s risk control system does not target marketing itself, but rather abnormal identity signals and abnormal behavior patterns. Therefore, sustainable and secure operation depends on three fundamentals: isolated environment, authentic identity, and stable behavior.
This article systematically explains the underlying registration logic, phased warm-up strategy, content operation standards, and suspension prevention principles to help B2B professionals build a low-risk, long-term operating system.
I. How to Successfully Register a LinkedIn Account
1.Stable and Clean Environment
Device and Network
- Use a device that has never registered or been suspended on LinkedIn.
- Keep the IP independent and clean.
- Avoid frequent switching between countries or regions.
- One account should correspond to one fixed IP environment.
Device fingerprints and IP access history are recorded long term. Once associated with abnormal history, changing email or phone number cannot eliminate the impact.
1.1 Obtain a residential proxy
Step 1: Log in to the IPFoxy dashboard and select residential proxy in your target region or country.
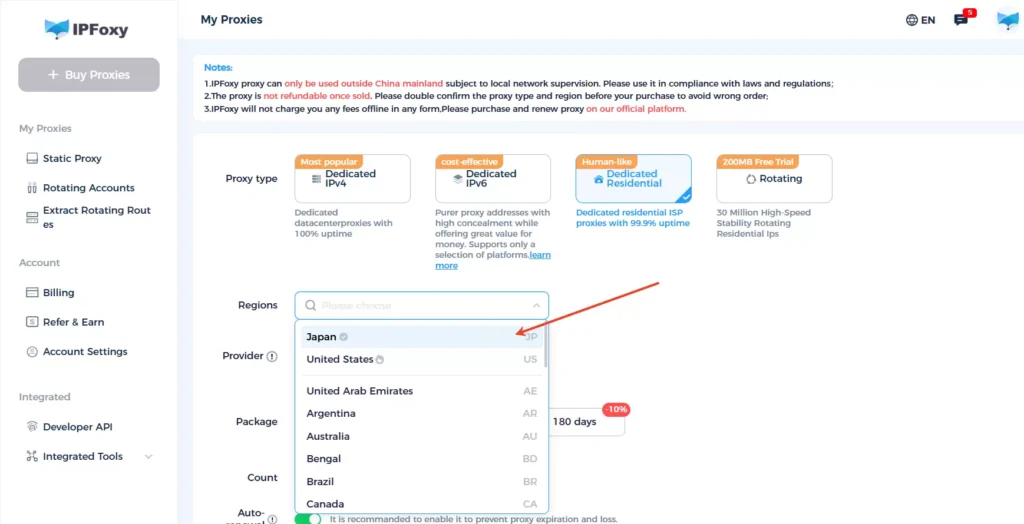
Step 2: After purchase, enter “Proxy Management” on the left panel.
- Retrieve IP address, port, username, and password.
- Configure the proxy on your mobile device or Anti-detect browser.
After configuration, your environment becomes stable and suitable for registering LinkedIn.
2.Registration Profile Standards
- Email: It is recommended to use a new Gmail or Outlook account. Other email providers may work, but stability and trust scores can be lower.
- Phone number: Use a number that has never been linked to LinkedIn. Avoid cross-account associations.
- Name: Must be your real name. LinkedIn is a real-name professional platform. Fake names significantly reduce trust scores.
- Company and job information: Must be real and verifiable. Avoid fabricated companies or vague job titles.
Practical summary: LinkedIn’s risk control relies on a comprehensive behavioral model rather than single-point verification. The registration phase determines your initial trust score. The system evaluates device fingerprint, network environment, email credibility, phone history, and profile authenticity. Therefore, prioritize security and compliance during registration.
II. LinkedIn Early-Stage Account Warm-Up Strategy
Phased Warm-Up Process
Phase 1 (Days 1–7): Silent Period
The goal is to establish basic browsing history and profile weight.
Actions:
- Complete profile elements gradually (profile photo, banner, skills).
- Use a professional business photo with a clean background.
- Link real company pages and naturally embed industry keywords.
- Structure your summary in three parts: personal introduction + industry experience + core business.
- Log in at least once daily.
- Browse industry-related content for 5–10 minutes.
- Do not like, comment, add connections, or post updates.
The focus is building a natural browsing footprint.
Phase 2 (Days 8–14): Light Interaction Period
Goal: Build an initial engagement model.
- Like at least five posts daily.
- Follow official accounts such as LinkedIn News.
- Track industry-related content.
- Leave a small number of high-quality comments.
Interactions must provide informational value and avoid template or promotional language.
Phase 3 (After Day 15): Stable Growth Period
Goal: Enter natural expansion stage.
- Add no more than 10 new connections per day.
- Publish 1–2 professional posts per week.
- Increase weekly interaction volume gradually by around 30 percent.
LinkedIn is highly sensitive to sudden spikes in activity. Maintain progressive growth.
Core Principles of LinkedIn Warm-Up
Stability First
The first 20 days are highly sensitive. The system monitors whether behavior matches natural user patterns. Avoid high-frequency, bulk, or abrupt actions.
Red-line behaviors include:
- Frequent changes to name, company, or job title.
- Bulk adding connections in a short time.
- Using automation plugins or scripts.
- Mass profile viewing or repeated visits.
- Sending bulk promotional messages.
- Copying or repeatedly posting identical content.
- Continuous high-frequency likes or follows.
Environment Isolation
If environment overlap or frequent changes occur, the system reassesses account risk.
Recommendations:
- Use a fixed device.
- Use a fixed IP address.
- Avoid switching between countries frequently.
- For multi-account management, use an Anti-detect browser or separate devices.
Ideal structure: One account = one device + one independent IP.
The IP should be a residential proxy with low fraud risk. Some operators choose providers such as IPFoxy to obtain cleaner IP resources. The core principle is stability and cleanliness.
Detection method:
Using a residential proxy from IPFoxy as an example, IP detection tools may show a fraud score of 0 and a low risk percentage, indicating a relatively clean IP.
Recommendations:
- Set random time intervals between actions (for example, 2–15 minutes).
- Avoid rapid consecutive operations.
- Maintain stable daily usage duration.
- Do not complete large volumes of actions in a short period.
The closer your behavior matches a real professional user, the lower the risk.
III. Advanced LinkedIn Growth Strategy
After completing the silent and stable activity stages, the account usually gains basic weight and trust. This is when you enter the expansion phase. The focus shifts to professional authority and natural business connection building.
Content Strategy: Build a Professional Positioning
Publish 2–3 vertical industry posts per week consistently.
Content directions:
- Industry trend analysis.
- Client cooperation cases (without sensitive information).
- Practical operational insights and process breakdowns.
The emphasis is professional credibility rather than marketing tone. Continuous vertical output helps the system assign industry labels and attract precise audiences organically.
Proactive Outreach: Engage Before Connecting
Instead of directly sending connection requests:
- Search for target prospects using keywords.
- Review their profiles.
- Like or comment on their posts with genuine interaction.
- Send a personalized invitation after 1–3 days.
The key is contextual relevance, such as referencing their content or shared industry challenges. This significantly improves acceptance rates compared to cold requests.
Tool Assistance: Expand Efficiency After Stability
Once the account is stable, auxiliary tools can improve efficiency under compliance principles, such as extracting publicly available contact information.
However, tools are efficiency amplifiers, not substitutes for trust and positioning. Without early-stage authority building, relying solely on tools often results in low conversion and higher risk.
The overall logic:
Build trust in early stages → Form stable behavior patterns → Deliver value and expand naturally.
Accounts that survive long term always grow steadily, maintain vertical content focus, and behave naturally instead of pursuing aggressive short-term growth.
IV. Frequently Asked Questions
Consistency matters more than frequency. One to two high-quality posts per week are sufficient. Maintain thematic continuity. Your profile should clearly communicate within three seconds what you offer, who you serve, and what value clients gain.
It depends on your target audience’s local active hours. For B2B clients, common active times are 9–11 AM and 2–4 PM local time. Test for two to three weeks, track engagement rates, and then standardize your posting schedule.
Generally after 30 days. The first 30 days are behavioral modeling periods. Adding connections aggressively too early may trigger risk control. LinkedIn is a trust-accumulation platform rather than a short-term viral platform.
Conclusion
In foreign trade and global markets, the difficulty of LinkedIn lies not in acquiring leads but in maintaining long-term account security. The platform evaluates identity authenticity and behavioral stability.
Registration requires independent devices and IP environments with authentic profile information. Warm-up must follow phased rhythm and avoid sudden spikes. Later stages focus on building trust through consistent professional content.
The fundamental logic is simple: clean environment, natural behavior, and long-term accumulation rather than aggressive short-term growth.


